A financially-motivated ransomware group known as Clop or TA505 has recently been exploiting a zero-day vulnerability in Progress Software’s MOVEit file transfer service. These exploits have resulted in a significant compromise of MOVEit databases and have had far-reaching consequences for multiple victims.
“TA505 is a cyber criminal group that has been active since at least 2014. TA505 is known for frequently changing malware, driving global trends in criminal malware distribution, and ransomware campaigns involving Clop.” - Group TA505: MITRE ATT&CK
A timeline of the 2023 MOVEit cyber attack
June 1: MOVEit’s vulnerability is flagged by cyber security researchers and the US government. MOVEit issues a patch for the software vulnerability.
June 5: Payroll provider Zellis announces that it was impacted by the MOVEit cyber attack. Companies including the BBC, Boots and British Airways suffer data breaches as a result.
June 7: Ransomware gang Clop issues a threat to victims to contact them by June 16, or their data will be posted online.
June 7: CISA and the FBI announces a US$10 million reward for “information linking the Clop gang or any other malicious cyber actors targeting US critical infrastructure to a foreign government”.
June 8: Professional services network and accounting firm, Ernst & Young (EY) announces that it was impacted by the MOVEit cyber attack. As a result, Health Service Ireland (HSE) suffered a data breach.
June 12: British communications watchdog Ofcom announces that it was a victim of the MOVEit cyber attack, causing a data breach that affected 412 employees.
June 14: Clop begins to post the profiles of companies allegedly breached during the cyber attack launched against MOVEit on its data leak website. Clop does not leak any of the stolen data.
June 15: CISA announces it is working with “multiple [US] federal agencies” that have been impacted by the MOVEit cyber attack. Affected agencies include two Department of Energy entities.
June 19: Accounting firm PriceWaterhouseCoopers (PwC) announces it was impacted by the MOVEit cyber attack
June 21: Clop claims to not have access to data from the BBC, Boots and BA that was thought to be stolen in the MOVEit cyber attack
June 23: PBI Research Services announces that the data of 4.75 million people was stolen from three of its clients (Genworth Financial, Wilton Reassurance and California Public Employees’ Retirement System (CalPERS)) because of the MOVEit cyber attack. Data stolen during the breach includes social security numbers, names, dates of birth and zip codes.
June 27: Seimens Energy and Schneider Electric both state they have been affected by the MOVEit cyber attack. Seimens says “no critical data [was] compromised” during the breach of its systems. Schneider Electric announces that, once it was made aware of the breach, it “promptly deployed available mitigations to secure data and infrastructure” and that its cyber security team is “currently investigating” the cyber attack.
Credit: Olivia Powell
IOTW: A full timeline of the MOVEit cyber attack
Initial Attack and Data Compromises
On June 5, several organizations disclosed that their employees’ personally identifiable information (PII) had been compromised. The attack initially targeted Zellis, a UK-based payroll provider that uses MOVEit and became vulnerable due to the identified security flaw. Clop ransomware claimed responsibility on June 6, stating on its dark web site that it successfully exploited the MOVEit vulnerability to exfiltrate data from numerous organizations. As a result, various cyber authorities, threat hunters, and security researchers are actively investigating and monitoring for potential new victims.
Anticipating Widespread Exploitation
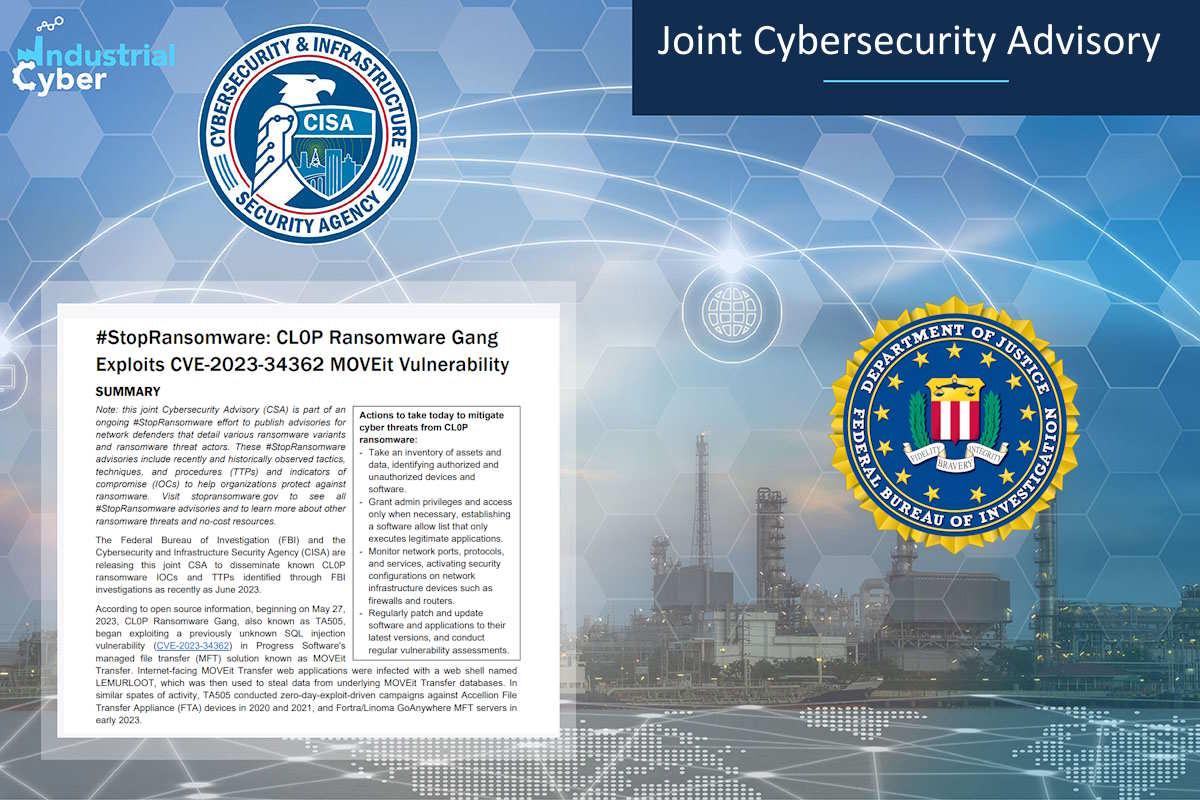
A joint advisory from the Cybersecurity and Infrastructure Security Agency (CISA) and the FBI, issued on June 7, warns that based on TA505’s past campaigns and the speed at which they exploited this vulnerability, widespread exploitation of unpatched software services in both private and public networks is anticipated.
Impact on High-Profile Organizations
High-profile organizations such as British Airways and the BBC have come forward as victims of the follow-on attack, affecting at least eight Zellis customers. British Airways is currently notifying employees affected by the compromise of their PII, while the BBC is conducting an investigation to determine the extent of the breach. The government of Nova Scotia, which also uses MOVEit, discovered that residents’ PII was compromised.
Extent of Affected Users
While the exact number of companies currently using MOVEit and the total count of victims have not been disclosed by Progress, the company has hundreds of thousands of customers, including 1,700 software companies and 3.5 million developers, as reported in its filing with the Securities and Exchange Commission.
Patching and Vulnerability Details
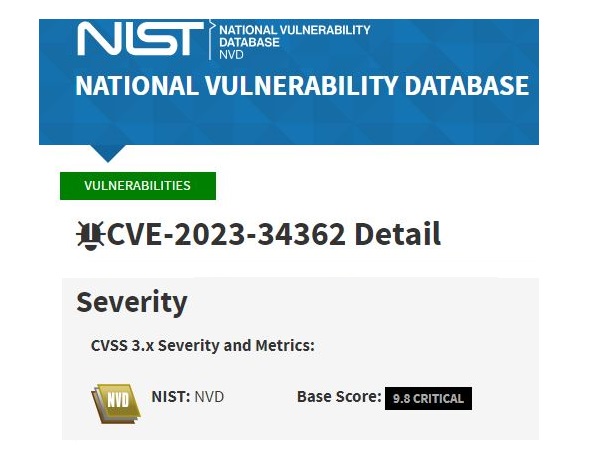
Progress publicly disclosed the zero-day vulnerability on May 31, identifying it as CVE-2023-34362 on June 2. The vulnerability affects both on-premises and cloud-based versions of MOVEit. Promptly, Progress released patches for on-premises versions and applied fixes to cloud test servers on June 1. Third-party validations have been conducted to ensure the effectiveness of the patch.
NIST: NVD
Base Score: 9.8 CRITICAL
Vector: CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
Ongoing Investigation and Collaboration
Multiple entities, including CISA, CrowdStrike, Mandiant, Microsoft, Huntress, and Rapid7, are collaborating with Progress in incident response and ongoing investigations to mitigate the effects of the attacks.
Previous Exploits and Attribution
This incident marks the third high-profile zero-day vulnerability linked to a file-transfer service this year. Clop, the group behind the attacks, has also exploited zero-day vulnerabilities in Fortra’s GoAnywhere file-transfer service in March and conducted a zero-day exploit-driven campaign against Accellion file transfer devices in 2020 and 2021. While researchers have differing opinions on the attribution of these attacks, indications point to Clop ransomware or its affiliates. Mandiant has identified a new threat cluster called UNC4857 (now merged into FIN11), known for exploiting zero-day vulnerabilities in file transfer systems. Microsoft attributes the attacks to Clop, specifically identifying the group as Lace Tempest under its threat actor naming system. Huntress has provided evidence suggesting that the web shell indicator of compromise shared by Progress and security researchers is not essential for compromising the MOVEit software.
BleepingComputer: Fortra shares findings on GoAnywhere MFT zero-day attacks
Mandiant: Zero-Day Vulnerability in MOVEit Transfer Exploited for Data Theft
Microsoft: How Microsoft names threat actors
Patching Additional Vulnerabilities
Progress has acknowledged the findings and released a patch for additional vulnerabilities discovered by Huntress. The investigation is ongoing, and there is currently no indication of exploitation of these newly discovered vulnerabilities. However, the potential for other attacks or consequences exists due to the identified arbitrary code execution attack vector.
Significance of Exploited Vulnerabilities
The recent attacks on MOVEit and its customers highlight the significance of exploited vulnerabilities as the primary cause of ransomware incidents. John Shier, field CTO at Sophos, emphasizes the importance of addressing vulnerabilities promptly to prevent such incidents in the future.
Additional References:
Progress MOVEit Community Article
John Hammond YT - MOVEit Transfer Exploitation (my API presentation recording)
1
2
3
4
┌──(root㉿servver)-[~]
└─$ cat howtocybersecurity.txt
- ## unplug the internet
-